In an era where data is often described as the new oil, the responsibility of handling it has never been greater. For Australian businesses, the recruitment process involves collecting some of the most sensitive information an individual can provide: their criminal history, financial records, and personal identity documents. Understanding the official data handling standards, including the Data Privacy Rules in Employee Background Verification, is not just a matter of legal compliance; it is a fundamental part of building a culture of trust and integrity.
As cyber threats evolve and privacy regulations tighten, employers must be more vigilant than ever. A single data breach or a mishandled background check can lead to devastating consequences, from multi-million dollar fines to a permanent loss of candidate trust.
The Foundation: The Privacy Act 1988 and the APPs
The primary legislation governing how personal information is handled in Australia is the Privacy Act 1988. Central to this Act are the 13 Australian Privacy Principles (APPs), which set out the standards for the collection, use, disclosure, and storage of personal data.
When it comes to official data handling standards, the APPs provide a clear roadmap for employers. While there is an employee records exemption in the Act, it is often misunderstood. Adhering to the Data Privacy Rules in Employee Background Verification is crucial to ensure compliance.
This exemption generally applies to the handling of records for current or former employees in relation to their employment. However, it does not typically apply to the recruitment phase or to the handling of data for unsuccessful candidates.
Employers need to familiarize themselves with the Data Privacy Rules in Employee Background Verification to avoid potential legal issues and maintain candidate trust.
Key Privacy Principles for Background Screening
1.Openness and Transparency: You must have a clearly defined privacy policy that explains how you handle background check data.
2.Collection of Solicited Personal Information: You should only collect information that is reasonably necessary for the role.
3.Notification of Collection: You must inform the candidate that their data is being collected and for what purpose.
4.Security of Personal Information: You are legally obligated to protect the data from unauthorised access, modification, or disclosure.
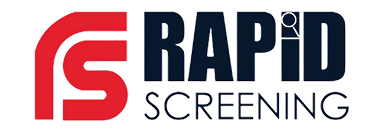
Essential Data Privacy Rules in Employee Background Verification
To maintain a compliant and secure screening process, Australian employers must adhere to several critical rules.
1. Informed Consent is Non-Negotiable
One of the most important official data handling standards is the requirement for explicit, written consent. You cannot legally initiate a police check, credit check, or any other sensitive verification without the candidate’s permission. This consent must be informed, meaning the candidate understands exactly what information is being sought and how it will be used.
2. The Principle of Data Minimisation
Just because you can check something doesn’t mean you should. Data minimisation is a core tenet of modern privacy law. Employers should only collect the specific data points necessary to assess a candidate’s suitability for a particular role. For example, a high-level security clearance might require a deep dive into financial history, whereas a retail role likely does not.
3. Secure Storage and Encryption
Under the official data handling standards, sensitive documents like birth certificates, passports, and criminal history results must be stored in a secure environment. This means using encrypted digital storage and ensuring that access is restricted to only those who need to know.
| Data Type | Sensitivity Level | Key Privacy Requirement |
| Criminal History (Police Check) | High | Explicit consent; secure disposal after use. |
| Identity Documents (Passport/DL) | High | Encrypted storage; verification via DVS. |
| Financial/Credit History | Medium-High | Only for relevant roles; strict access control. |
| Reference Check Notes | Medium | Subject to APP 12 (Access and Correction). |
| Medical/Health Information | High | Only if relevant to inherent job requirements. |
The Role of Accredited Providers in Data Security
Choosing the right partner for your background screening is a critical part of complying with data privacy rules in employee background verification. When you use an ACIC-accredited provider like Rapid Screening, you are leveraging a platform that has been built from the ground up with security in mind.
Why Accreditation Matters for Privacy
Accredited bodies must undergo rigorous auditing by the Australian Criminal Intelligence Commission (ACIC). This ensures that their systems meet the highest standards for:
•Data Encryption: Protecting information both in transit and at rest.
•Access Control: Ensuring that only authorised personnel can view sensitive results.
•Audit Trails: Maintaining a record of who accessed what data and when.
By using an accredited provider, you are not just getting a faster check; you are ensuring that you are meeting your legal obligations under the official data handling standards.
Navigating the Employee Records Exemption
As mentioned earlier, the employee records exemption is a common point of confusion. It is vital for HR professionals to understand that this exemption is narrow. It only applies to acts or practices that are directly related to a current or former employment relationship.
In the context of official data handling standards, this means:
•During Recruitment: The exemption does not apply. You must follow the APPs for all
candidates.
•Unsuccessful Candidates: You must handle their data according to the APPs, which usually means destroying or de-identifying the information once the hiring decision is made.
•Successful Hires: Once the candidate becomes an employee, the information may become part of their employee record, but it must still be handled with extreme care.
The Importance of Data Disposal
A key part of the official data handling standards that is often overlooked is the secure disposal of information. Once a background check has served its purpose, the sensitive data should not be kept indefinitely.
For unsuccessful candidates, the best practice is to securely delete their background check results and identity documents as soon as the recruitment process is finalised. For successful hires, you should only retain the information that is necessary for the ongoing management of their employment.
Best Practices for Compliance with Data Privacy Rules in Employee Background Verification
To ensure your organisation remains on the right side of the law and maintains the trust of its candidates, we recommend implementing the following best practices:
1. Conduct a Privacy Impact Assessment (PIA)
Before implementing a new background screening process, conduct a PIA. This helps you identify potential privacy risks and implement strategies to mitigate them. It is a proactive way to ensure you are following the official data handling standards from day one.
2. Implement Privacy by Design
Privacy should not be an afterthought. When choosing a screening platform or designing your internal workflows, ensure that privacy is built into the process. This includes using automated systems that minimise human contact with sensitive data and ensuring that all data transfers are encrypted.
3. Train Your HR and Recruitment Teams
Your people are your first line of defence. Ensure that everyone involved in the hiring process understands the official data handling standards. They should know how to handle sensitive documents, how to obtain proper consent, and how to securely dispose of data.
| Step | Action | Privacy Goal |
| 1. Policy Review | Update your privacy policy to include background checks. | Transparency (APP 1) |
| 2. Consent Form | Create a clear, separate consent form for each check. | Informed Consent |
| 3. Vendor Audit | Ensure your screening provider is ACIC-accredited. | Data Security (APP 11) |
| 4. Access Control | Limit data access to specific HR personnel. | Confidentiality |
| 5. Data Disposal | Securely delete data for unsuccessful candidates. | Data Minimisation |
The Consequences of Mishandling Data
The official data handling standards are not just suggestions; they are legal requirements with significant teeth. In recent years, the Office of the Australian Information Commissioner (OAIC) has been given increased powers to penalise organisations that fail to protect personal information.
The consequences of a privacy breach can include:
•Civil Penalties: Fines for serious or repeated privacy breaches can reach up to $50 million or more for large corporations.
•Reputational Damage: A data breach can permanently tarnish your brand, making it difficult to attract top-tier talent in the future.
•Legal Action: Candidates and employees may take legal action for damages resulting from a privacy breach.
By prioritising the official data handling standards, you are protecting your business from these significant risks.
Conclusion
The data privacy rules in employee background verification are the guardrails that ensure the Australian recruitment process remains fair, secure, and respectful of individual rights. By understanding your obligations under the Privacy Act, implementing best practices for data handling, and partnering with accredited experts, you can build a screening process that is a true asset to your business.
In a world where privacy is increasingly valued, being a privacy first employer is a significant competitive advantage. Protect your candidates, protect your data, and protect your business by making data privacy a cornerstone of your recruitment strategy.
Frequently Asked Questions (FAQs)
1. Can I share a candidate’s background check results with other departments?
Only if it is directly relevant to their role and you have the candidate’s consent. Under the official data handling standards, you should limit the disclosure of sensitive information to only those who absolutely need it for the hiring decision.
2. How long should I keep background check data for unsuccessful candidates?
The best practice is to securely dispose of this data as soon as the recruitment process is complete. Keeping sensitive data for people you haven’t hired increases your risk profile without providing any business benefit.
3. Does the employee records exemption cover the recruitment phase?
No. The exemption generally only applies once an employment relationship has been established. During the recruitment phase, you must comply with all the Australian Privacy Principles (APPs) as part of the official data handling standards.
4. What should I do if there is a data breach involving background check results?
You must follow the Notifiable Data Breaches (NDB) scheme. This involves assessing the breach, notifying the OAIC, and informing the affected individuals if the breach is likely to result in serious harm.
5. Are digital background check certificates secure?
Yes, provided they are issued by an accredited provider like Rapid Screening. Our digital certificates include security features like encryption and verification codes to ensure they are authentic and protected from unauthorised access, in line with data privacy rules in employee background verification.
6. Can a candidate request to see their background check results?
Yes. Under APP 12, individuals have a right to access the personal information that an organisation holds about them. This is a key part of the data privacy rules in employee background verification that ensures transparency and fairness.